Michael Rooney
1LT Cyber Capabilities Developer (Basic), US Army
About Me

I'm a 1LT in the US Army Cyber Branch and a student at Purdue University pursuing a Master of Science in Computer Science. While at Purdue, I am being co-advised by Prof. Dongyan Xu (Purdue) and Prof. Arslan Khan (Penn State) on my research in semi-automatic rehosting of flight-control firmware and embedded system reverse engineering.
During my time at Purude, I have been fortunate to work as a part of the FIRE project, a DARPA project that is focused on rapid reverse engineering and exploitation of cyber-physical systems. My goal during my time at Purdue is to leverage my expertise in virtualization and reverse engineering to develop a template-based framework for semi-automatic rehosting of popular flight-control firmware.
Areas of Expertise
Academic Portfolio
Education
B.S. in Computer Science with Honors
United States Military Academy at West Point
2020-2024
I graduated Top 50 in my class overall and was the #2 ranked cadet in my class for computer science. My research focused on leveraging Single Board Computers for efficient monitoring of cyber-physical systems on the edge.
Master of Science in Computer Science (Thesis)
Purdue University
2024-2026
Currently pursuing a Master of Science in Computer Science with a focus on semi-automatic rehosting of flight-control firmware and embedded system reverse engineering.
Research Experience
FIRE: Faithful Integrated Reverse-engineering and Exploitation
Rehosting and Simulation ExpertPurSec Lab, Purdue University
August 2024 - Present
While on the FIRE program, I have been tasked as the primary engineer in charge of developing co-simulation platforms for systems-under-test (SUTs) in order to facilitate the reverse engineering and exploitation of the SUTs. Specifically, I performed firmware reverse engineering and leveraged slice-based execution to hook execution of the firmware at the HAL-level and faithfully emulate the true behavior of the SUT. Additionally, I created a time-synchronization bridge between the QEMU simulation of the firmware and the physical simulation, Gazebo, to provide our security researchers with a rapidly-reusable environment to test cyber-physical vulnerability hypotheses. My research experience on this project has been invaluable and we are currently working on making this work more automated and generalizable.
Real-Time Anomaly Detection for West Point's 1:1000 EmulatedSmart Grid
Capstone Team MemberUSMA EECS Department
August 2023 - May 2024
During this capstone project, I was able to transition much of my research from the previous year and a half and apply it to a real-world application. My role was to develop a system that would be able to detect anomalies in the smart grid in real-time leveraging a linear state estimator that I had written using the Rust programming language the semester prior. While performing linear state estimation on the power grid data in real-time (82 measurements every 16.67ms), I was also in charge of developing an operator interface that would allow the user to view the state of the system and the anomalies that were detected.
Publications
A Comparative Study of Programming Languages for a Real-Time Smart Grid Application
2023 IEEE Green Energy and Smart Systems Conference (IGESSC)
Evaluating FFT Performance of the C and Rust Languages on Raspberry Pi Platforms
2023 57th annual conference on information sciences and systems (CISS)
Project Portfolio
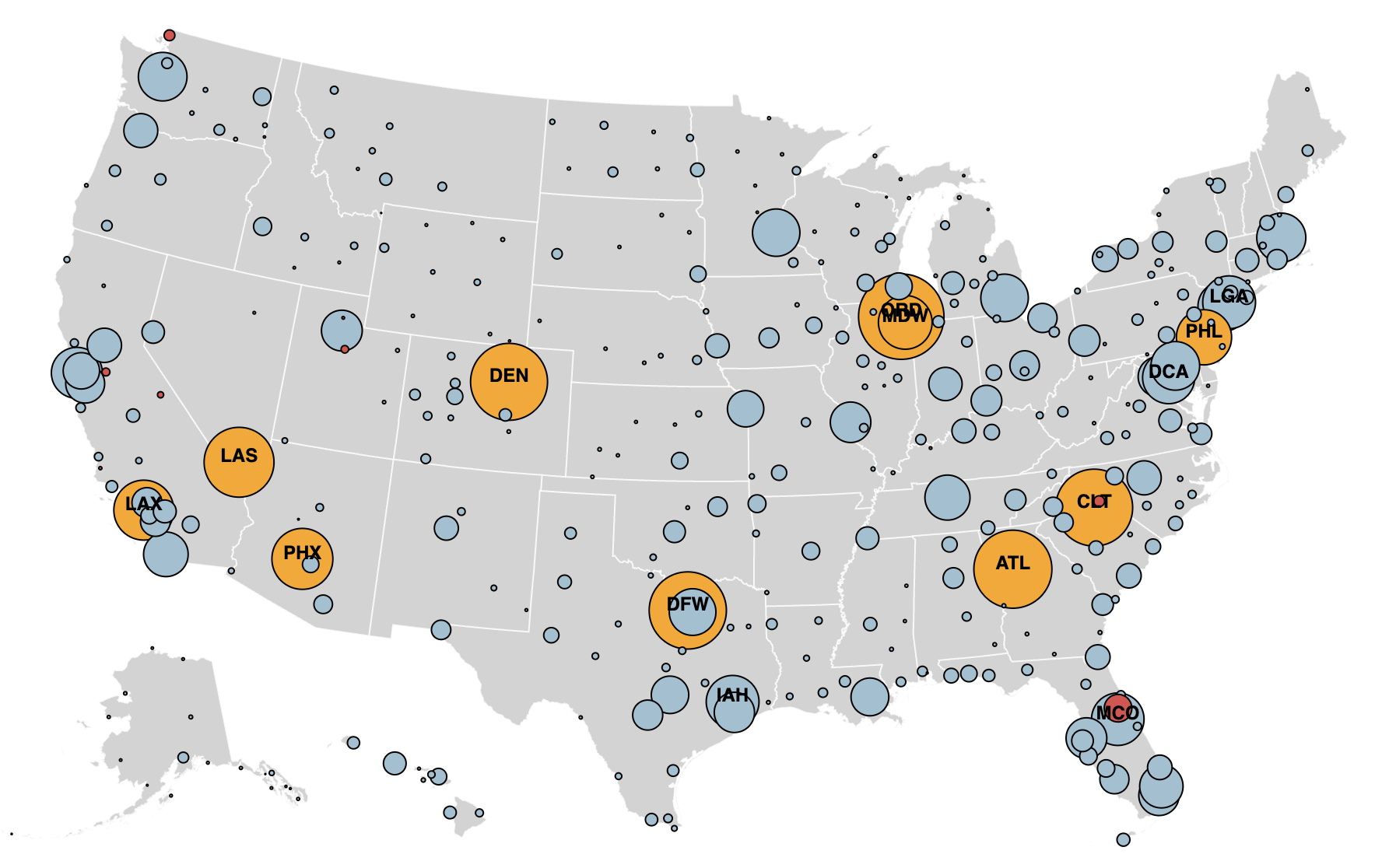
COVID-19 Data Visualization
A data visualization project analyzing COVID-19's affect on air traffic in the United States. This project relied on D3 and Observable notebooks to create the visualizations. More information on the project can be found on the interactive visualization website.
Get In Touch
I'm always open to discussing research opportunities, collaborations, or interesting projects. Feel free to reach out to me via email, LinkedIn, or GitHub.